Will They Marry? Linux and Rust in 2026
Rust is now permanent in the Linux kernel. After 3 years of testing, production Android deployments, and Debian mandating Rust for APT, the…

Rust is now permanent in the Linux kernel. After 3 years of testing, production Android deployments, and Debian mandating Rust for APT, the experiment concluded at Tokyo summit.
The experiment is over. Three years. Thirteen major kernel versions. One verdict: Rust stays.
At the Linux Kernel Maintainers Summit in Tokyo last December, Miguel Ojeda delivered the words that ended years of debate.
If you’ve been building systems on Linux (and who hasn’t), this changes how kernel development works going forward. Not whether it changes. How fast.
The Tokyo Verdict
“The experiment is done. Rust is here to stay.”
Miguel Ojeda, the Rust for Linux project lead, made this announcement at the December 2025 Maintainers Summit in Tokyo. This wasn’t a vote. It wasn’t a proposal. It was a conclusion based on evidence.
Rust support merged in kernel v6.1 back in 2022. The question then: Is Rust suitable for kernel development? The criteria were practical. Can we maintain it? Can we build with it? Does it actually prevent bugs?
Three years later, the data answered yes to all three.
If you’ve worked with production systems, you know how rare this is. Technology experiments usually die quiet deaths. This one shipped to millions of devices.

I am a human writer who gets motivated to write more with your support! You don’t need to pay. I just need your clap 👏 if you like my story and comment ✍️ if you want to say something. You can follow me on Medium, LinkedIn, Instagram and X.
Production Reality: Android 16
This isn’t theory anymore. Android 16 devices shipping on Linux 6.12 include the Rust ashmem allocator in production. That’s memory allocation code running on millions of phones.
For context: ashmem (Anonymous Shared Memory) handles how Android apps share memory. It’s not experimental feature code. It’s core infrastructure.
When Google puts Rust in the memory subsystem of production Android, the debate about “production readiness” ends. You can argue theory all day. Shipping code on consumer devices is a different conversation entirely.
This matters because memory safety bugs account for roughly 70% of security vulnerabilities in large C/C++ codebases. Microsoft, Google, and Apple have all published data supporting this. The kernel is no exception.
The Debian Signal
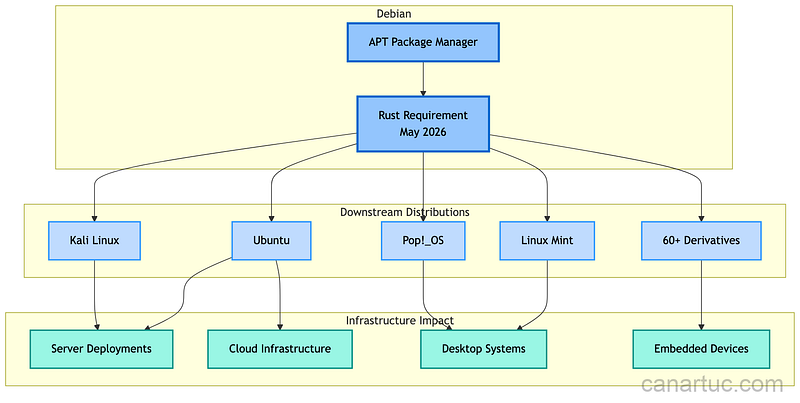
Debian’s announcement adds another dimension. Starting May 2026, APT requires Rust. Not optional. Not recommended. Required.
This affects the entire package management chain. Every Debian derivative (Ubuntu, Linux Mint, Pop!_OS, and dozens more) inherits this requirement. The ripple effects touch hundreds of millions of systems.
It’s no longer a technology choice. It’s an infrastructure reality.
What Actually Changed in v6.13
Linux 6.13 added over 3,000 lines of Rust code. Most of it is infrastructure: abstractions that let Rust code interact with kernel subsystems safely.
The additions include:
Kernel abstractions: Higher-level interfaces for memory management, locking primitives, and device registration. These translate C kernel APIs into Rust patterns.
Device driver foundations: Basic structures for writing peripheral drivers. Not fancy, but necessary groundwork.
Error handling patterns: Kernel-appropriate error types that map to existing return conventions.
This is foundation work. Not flashy features. The kind of infrastructure that makes future development faster.
The Ongoing Challenges
Permanence doesn’t mean problems solved. Two significant issues remain.
Toolchain coverage: Rust supports fewer CPU architectures than C. The kernel runs on everything from mainframes to microcontrollers. Rust compilation works on major architectures (x86_64, ARM64, RISC-V), but edge cases exist.
For embedded and specialized hardware, this creates practical constraints. If your target architecture lacks Rust support, C remains the only option.
Maintenance burden: The 2025 controversies were real. Some maintainers resigned over disagreements about Rust’s complexity. Others pushed back against additional toolchain requirements in their subsystems.
This isn’t unique to Rust. Any significant kernel change creates friction. What matters is whether the community moves forward despite disagreements. The Tokyo summit suggests it does.
What This Means for Practitioners
If you’re writing kernel code: Rust is now an option for new subsystems. Not required everywhere, but available.
If you’re maintaining production Linux systems: watch the Rust toolchain requirements. They affect build infrastructure and architecture support.
If you’re making technology decisions: the kernel’s adoption validates Rust for systems programming beyond web services and CLI tools. The safety benefits translate to infrastructure that matters.

The Bigger Picture
The kernel is infrastructure that infrastructure depends on. Every container, every cloud instance, every Android phone runs on it.
When this codebase embraces a language specifically designed to prevent memory safety bugs, it signals something broader. The tolerance for preventable vulnerabilities is decreasing. The tools to prevent them are maturing.
Rust in the kernel isn’t about replacing C. The millions of lines of existing C code aren’t going anywhere. It’s about having better options for new code. Particularly code where memory safety matters most.
The experiment started with a question: can Rust work in the kernel? Three years of evidence answered it. Now comes the harder part: making it work everywhere the kernel runs.
If this resonates with your experience in kernel development or systems programming, clap so other practitioners can find it. I’d like to know what I might be missing about the Rust adoption challenges in your specific context.
What’s your take on the Rust kernel adoption timeline? Are the toolchain limitations a significant concern for your use cases?
I am a human writer who gets motivated to write more with your support! You don’t need to pay. I just need your clap 👏 if you like my story and comment ✍️ if you want to say something. You can follow me on Medium, LinkedIn, Instagram and X.